Hallo Klaus,
danke fürs Mitdenken und Deinen Tipp. Leider scheint da alles ok zu sein: nach dem Löschen der Schlüsseltabelle ist die Datei /usr/local/etc/squid/squid.keytab gelöscht. Nach dem Neuerstellen ist sie wieder erzeugt, ein Test der Anmeldung schlägt aber genauso fehl wie bisher.
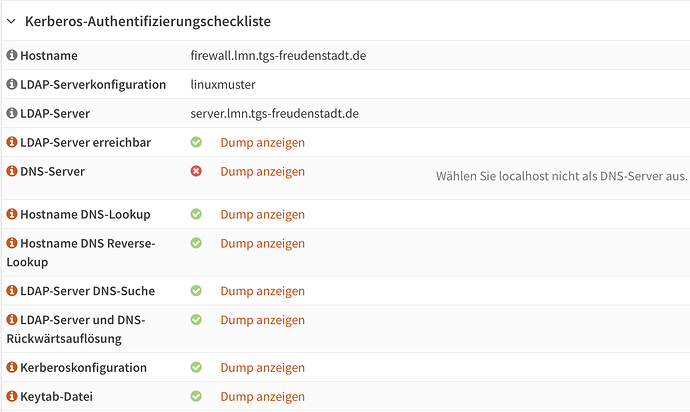
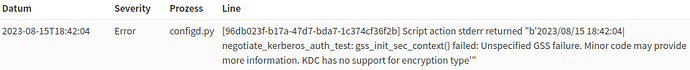
Ich habe in der Zwischenzeit weiter geschaut, was es sein kann, und m.E. deutet inzwischen alles darauf hin, dass sich die Kerberos-Encryption-Verfahren zwischen OpnSense und LMN7.2-Server nicht vertragen. Nach einem Anmeldeversuch über „Kerberos Anmeldung testen“ findet man im Log der OpnSense unter System: Protokolldateien: Backend:
Und auf dem LMN7.2-Server, dessen Samba Log level ich inzwischen auf 10 hoch gedreht habe findet man
[2023/08/15 18:42:04.069888, 10, pid=4304, effective(0, 0), real(0, 0)] ../../source4/kdc/kdc-server.c:281(kdc_tcp_call_loop)
Received krb5 TCP packet of length 271 from ipv4:10.32.1.254:53797
[2023/08/15 18:42:04.069928, 10, pid=4304, effective(0, 0), real(0, 0)] ../../source4/kdc/kdc-heimdal.c:81(kdc_process)
kdc_process: Received KDC packet of length 263 from ipv4:10.32.1.254:53797
[2023/08/15 18:42:04.069999, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: AS-REQ jhe@LMN.MEINE-SCHULE.DE from ipv4:10.32.1.254:53797 for krbtgt/LMN.MEINE-SCHULE.DE@LMN.MEINE-SCHULE.DE
[2023/08/15 18:42:04.070743, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.072085, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.072339, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.072494, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Client sent patypes: encrypted-timestamp, 150, 149
[2023/08/15 18:42:04.072519, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Looking for PKINIT pa-data -- jhe@LMN.MEINE-SCHULE.DE
[2023/08/15 18:42:04.072544, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Looking for ENC-TS pa-data -- jhe@LMN.MEINE-SCHULE.DE
[2023/08/15 18:42:04.072582, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: ENC-TS Pre-authentication succeeded -- jhe@LMN.MEINE-SCHULE.DE using aes256-cts-hmac-sha1-96
[2023/08/15 18:42:04.072634, 3, pid=4304, effective(0, 0), real(0, 0), class=auth_audit] ../../auth/auth_log.c:647(log_authentication_event_human_readable)
Auth: [Kerberos KDC,ENC-TS Pre-authentication] user [(null)]\[jhe@LMN.MEINE-SCHULE.DE] at [Tue, 15 Aug 2023 18:42:04.072626 UTC] with [aes256-cts-hmac-sha1-96] status [NT_STATUS_OK] workstation [(null)] remote host [ipv4:10.32.1.254:53797] became [LMN]\[jhe] [S-1-5-21-4239855724-3324929432-2762375390-1138]. local host [NULL]
{"timestamp": "2023-08-15T18:42:04.072703+0000", "type": "Authentication", "Authentication": {"version": {"major": 1, "minor": 2}, "eventId": 4624, "logonId": "f37a4952087e5875", "logonType": 3, "status": "NT_STATUS_OK", "localAddress": null, "remoteAddress": "ipv4:10.32.1.254:53797", "serviceDescription": "Kerberos KDC", "authDescription": "ENC-TS Pre-authentication", "clientDomain": null, "clientAccount": "jhe@LMN.MEINE-SCHULE.DE", "workstation": null, "becameAccount": "jhe", "becameDomain": "LMN", "becameSid": "S-1-5-21-4239855724-3324929432-2762375390-1138", "mappedAccount": "jhe", "mappedDomain": "LMN", "netlogonComputer": null, "netlogonTrustAccount": null, "netlogonNegotiateFlags": "0x00000000", "netlogonSecureChannelType": 0, "netlogonTrustAccountSid": null, "passwordType": "aes256-cts-hmac-sha1-96", "duration": 2792}}
[2023/08/15 18:42:04.072758, 4, pid=4304, effective(0, 0), real(0, 0), class=auth] ../../source4/auth/sam.c:203(authsam_account_ok)
authsam_account_ok: Checking SMB password for user jhe@LMN.MEINE-SCHULE.DE
[2023/08/15 18:42:04.072814, 5, pid=4304, effective(0, 0), real(0, 0), class=auth] ../../source4/auth/sam.c:137(logon_hours_ok)
logon_hours_ok: No hours restrictions for user jhe@LMN.MEINE-SCHULE.DE
[2023/08/15 18:42:04.072833, 5, pid=4304, effective(0, 0), real(0, 0), class=auth] ../../source4/auth/sam.c:1077(authsam_logon_success_accounting)
lastLogonTimestamp is 133364017681818390
[2023/08/15 18:42:04.073013, 5, pid=4304, effective(0, 0), real(0, 0), class=auth] ../../source4/auth/sam.c:962(authsam_update_lastlogon_timestamp)
sync interval is 14
[2023/08/15 18:42:04.073044, 5, pid=4304, effective(0, 0), real(0, 0), class=auth] ../../source4/auth/sam.c:979(authsam_update_lastlogon_timestamp)
randomised sync interval is 11 (-3)
[2023/08/15 18:42:04.073058, 5, pid=4304, effective(0, 0), real(0, 0), class=auth] ../../source4/auth/sam.c:985(authsam_update_lastlogon_timestamp)
old timestamp is 133364017681818390, threshold 133356481240728690, diff 7536441089700
[2023/08/15 18:42:04.073723, 10, pid=4304, effective(0, 0), real(0, 0)] ../../source4/dsdb/samdb/ldb_modules/acl.c:1279(acl_modify)
ldb:acl_modify: lastLogon
[2023/08/15 18:42:04.074259, 5, pid=4304, effective(0, 0), real(0, 0), class=dsdb_audit] ../../lib/audit_logging/audit_logging.c:95(audit_log_human_text)
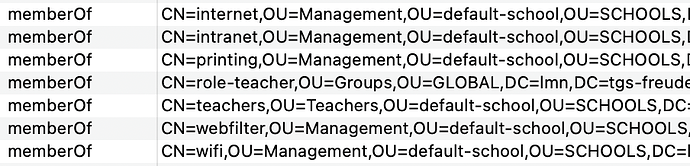
DSDB Change [Modify] at [Tue, 15 Aug 2023 18:42:04.074246 UTC] status [Success] remote host [Unknown] SID [S-1-5-18] DN [CN=jhe,OU=Teachers,OU=default-school,OU=SCHOOLS,DC=lmn,DC=meine-schule,DC=de] attributes [replace: lastLogon [133365985240728690] replace: logonCount [64]]
{"timestamp": "2023-08-15T18:42:04.074296+0000", "type": "dsdbChange", "dsdbChange": {"version": {"major": 1, "minor": 0}, "statusCode": 0, "status": "Success", "operation": "Modify", "remoteAddress": null, "performedAsSystem": false, "userSid": "S-1-5-18", "dn": "CN=jhe,OU=Teachers,OU=default-school,OU=SCHOOLS,DC=lmn,DC=meine-schule,DC=de", "transactionId": "48ff6230-ec72-479a-9604-14dcd9436718", "sessionId": "7602963a-2ea6-4553-a210-15b1142f47b2", "attributes": {"lastLogon": {"actions": [{"action": "replace", "values": [{"value": "133365985240728690"}]}]}, "logonCount": {"actions": [{"action": "replace", "values": [{"value": "64"}]}]}}}}
[2023/08/15 18:42:04.082102, 10, pid=4304, effective(0, 0), real(0, 0), class=dsdb_transaction_audit] ../../lib/audit_logging/audit_logging.c:95(audit_log_human_text)
DSDB Transaction [commit] at [Tue, 15 Aug 2023 18:42:04.082093 UTC] duration [9001]
{"timestamp": "2023-08-15T18:42:04.082133+0000", "type": "dsdbTransaction", "dsdbTransaction": {"version": {"major": 1, "minor": 0}, "action": "commit", "transactionId": "48ff6230-ec72-479a-9604-14dcd9436718", "duration": 9001}}
[2023/08/15 18:42:04.086334, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.086442, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: AS-REQ authtime: 2023-08-15T18:42:04 starttime: unset endtime: 2023-08-16T04:42:04 renew till: 2023-08-16T18:42:04
[2023/08/15 18:42:04.086468, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Client supported enctypes: aes256-cts-hmac-sha1-96, arcfour-hmac-md5, using aes256-cts-hmac-sha1-96/aes256-cts-hmac-sha1-96
[2023/08/15 18:42:04.086499, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Requested flags: renewable-ok
[2023/08/15 18:42:04.086888, 3, pid=4304, effective(0, 0), real(0, 0)] ../../source4/samba/service_stream.c:67(stream_terminate_connection)
stream_terminate_connection: Terminating connection - 'kdc_tcp_call_loop: tstream_read_pdu_blob_recv() - NT_STATUS_CONNECTION_DISCONNECTED'
[2023/08/15 18:42:04.086945, 10, pid=4304, effective(0, 0), real(0, 0)] ../../lib/messaging/messages_dgm_ref.c:163(msg_dgm_ref_destructor)
msg_dgm_ref_destructor: refs=0x56087a21efc0
[2023/08/15 18:42:04.092081, 10, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dns_server.c:540(dns_udp_call_loop)
Received DNS UDP packet of length 48 from ipv4:10.32.1.254:15552
[2023/08/15 18:42:04.092131, 8, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../lib/util/util.c:585(dump_data_dbgc)
[0000] 4F 04 01 00 00 01 00 00 00 00 00 00 06 73 65 72 O....... .....ser
[0010] 76 65 72 03 6C 6D 6E 10 74 67 73 2D 66 72 65 75 ver.lmn.
[0020] 64 65 6E 73 74 61 64 74 02 64 65 00 00 01 00 01 .de.....
[2023/08/15 18:42:04.092176, 8, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dns_server.c:153(dns_process_send)
{"timestamp": "2023-08-15T18:42:04.082133+0000", "type": "dsdbTransaction", "dsdbTransaction": {"version": {"major": 1, "minor": 0}, "action": "commit", "transactionId": "48ff6230-ec72-479a-9604-14dcd9436718", "duration": 9001}}
[2023/08/15 18:42:04.086334, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.086442, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: AS-REQ authtime: 2023-08-15T18:42:04 starttime: unset endtime: 2023-08-16T04:42:04 renew till: 2023-08-16T18:42:04
[2023/08/15 18:42:04.086468, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Client supported enctypes: aes256-cts-hmac-sha1-96, arcfour-hmac-md5, using aes256-cts-hmac-sha1-96/aes256-cts-hmac-sha1-96
[2023/08/15 18:42:04.086499, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Requested flags: renewable-ok
[2023/08/15 18:42:04.086888, 3, pid=4304, effective(0, 0), real(0, 0)] ../../source4/samba/service_stream.c:67(stream_terminate_connection)
stream_terminate_connection: Terminating connection - 'kdc_tcp_call_loop: tstream_read_pdu_blob_recv() - NT_STATUS_CONNECTION_DISCONNECTED'
[2023/08/15 18:42:04.086945, 10, pid=4304, effective(0, 0), real(0, 0)] ../../lib/messaging/messages_dgm_ref.c:163(msg_dgm_ref_destructor)
msg_dgm_ref_destructor: refs=0x56087a21efc0
[2023/08/15 18:42:04.092081, 10, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dns_server.c:540(dns_udp_call_loop)
Received DNS UDP packet of length 48 from ipv4:10.32.1.254:15552
[2023/08/15 18:42:04.092131, 8, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../lib/util/util.c:585(dump_data_dbgc)
[0000] 4F 04 01 00 00 01 00 00 00 00 00 00 06 73 65 72 O....... .....ser
[0010] 76 65 72 03 6C 6D 6E 10 74 67 73 2D 66 72 65 75 ver.lmn.
[0020] 64 65 6E 73 74 61 64 74 02 64 65 00 00 01 00 01 .de.....
[2023/08/15 18:42:04.092176, 8, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dns_server.c:153(dns_process_send)
[2023/08/15 18:42:04.092330, 1, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../librpc/ndr/ndr.c:410(ndr_print_debugc)
&state->in_packet: struct dns_name_packet
id : 0x4f04 (20228)
operation : 0x0100 (256)
0x00: DNS_RCODE (0)
0: DNS_FLAG_RECURSION_AVAIL
1: DNS_FLAG_RECURSION_DESIRED
0: DNS_FLAG_TRUNCATION
0: DNS_FLAG_AUTHORITATIVE
0x00: DNS_OPCODE (0)
0: DNS_FLAG_REPLY
qdcount : 0x0001 (1)
ancount : 0x0000 (0)
nscount : 0x0000 (0)
arcount : 0x0000 (0)
questions: ARRAY(1)
questions: struct dns_name_question
name : 'server.lmn.meine-schule.de'
question_type : DNS_QTYPE_A (0x1)
question_class : DNS_QCLASS_IN (0x1)
answers: ARRAY(0)
nsrecs: ARRAY(0)
additional: ARRAY(0)
[2023/08/15 18:42:04.093190, 10, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dnsserver_common.c:245(dns_common_lookup)
dns_common_lookup: DNS timing: result: [WERR_OK] duration: (204) zone: [] name: [DC=server,DC=lmn.meine-schule.de,CN=MicrosoftDNS,DC=DomainDnsZones,DC=lmn,DC=meine-schule,DC=de] data: []
[2023/08/15 18:42:04.093219, 10, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dnsserver_common.c:626(dns_common_wildcard_lookup)
dns_common_wildcard_lookup: DNS timing: result: [WERR_OK] duration: (232) zone: [] name: [DC=server,DC=lmn.meine-schule.de,CN=MicrosoftDNS,DC=DomainDnsZones,DC=lmn,DC=meine-schule,DC=de] data: []
[2023/08/15 18:42:04.093244, 10, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dns_query.c:361(add_zone_authority_record)
Creating zone authority record for 'lmn.meine-schule.de'
[2023/08/15 18:42:04.093647, 10, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dnsserver_common.c:245(dns_common_lookup)
dns_common_lookup: DNS timing: result: [WERR_OK] duration: (274) zone: [] name: [DC=@,DC=lmn.meine-schule.de,CN=MicrosoftDNS,DC=DomainDnsZones,DC=lmn,DC=meine-schule,DC=de] data: []
MicrosoftDNS,DC=DomainDnsZones,DC=lmn,DC=meine-schule,DC=de] data: []
[2023/08/15 18:42:04.093678, 8, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../source4/dns_server/dns_server.c:263(dns_process_recv)
[2023/08/15 18:42:04.093690, 1, pid=4312, effective(0, 0), real(0, 0), class=dns] ../../librpc/ndr/ndr.c:410(ndr_print_debugc)
&state->out_packet: struct dns_name_packet
id : 0x4f04 (20228)
operation : 0x8580 (34176)
0x00: DNS_RCODE (0)
1: DNS_FLAG_RECURSION_AVAIL
1: DNS_FLAG_RECURSION_DESIRED
0: DNS_FLAG_TRUNCATION
1: DNS_FLAG_AUTHORITATIVE
0x00: DNS_OPCODE (0)
1: DNS_FLAG_REPLY
qdcount : 0x0001 (1)
ancount : 0x0001 (1)
nscount : 0x0001 (1)
arcount : 0x0000 (0)
questions: ARRAY(1)
questions: struct dns_name_question
name : 'server.lmn.meine-schule.de'
question_type : DNS_QTYPE_A (0x1)
question_class : DNS_QCLASS_IN (0x1)
answers: ARRAY(1)
answers: struct dns_res_rec
name : 'server.lmn.meine-schule.de'
rr_type : DNS_QTYPE_A (0x1)
rr_class : DNS_QCLASS_IN (0x1)
ttl : 0x00000384 (900)
length : 0xffff (65535)
rdata : union dns_rdata(case 0x1)
ipv4_record : 10.32.1.1
unexpected : DATA_BLOB length=0
nsrecs: ARRAY(1)
nsrecs: struct dns_res_rec
name : 'lmn.meine-schule.de'
rr_type : DNS_QTYPE_SOA (0x6)
rr_class : DNS_QCLASS_IN (0x1)
ttl : 0x00000e10 (3600)
length : 0xffff (65535)
rdata : union dns_rdata(case 0x6)
soa_record: struct dns_soa_record
mname : 'server.lmn.meine-schule.de'
rname : 'hostmaster.lmn.meine-schule.de'
serial : 0x00000006 (6)
refresh : 0x00000384 (900)
retry : 0x00000258 (600)
expire : 0x00015180 (86400)
minimum : 0x00000e10 (3600)
unexpected : DATA_BLOB length=0
additional: ARRAY(0)
[2023/08/15 18:42:04.094710, 10, pid=4304, effective(0, 0), real(0, 0)] ../../lib/messaging/messages_dgm_ref.c:92(messaging_dgm_ref)
messaging_dgm_ref: messaging_dgm_get_unique returned Success
[2023/08/15 18:42:04.094768, 10, pid=4304, effective(0, 0), real(0, 0)] ../../lib/messaging/messages_dgm_ref.c:109(messaging_dgm_ref)
messaging_dgm_ref: unique = 10004098688105350037
[2023/08/15 18:42:04.094862, 10, pid=4304, effective(0, 0), real(0, 0)] ../../source4/kdc/kdc-server.c:281(kdc_tcp_call_loop)
Received krb5 TCP packet of length 1957 from ipv4:10.32.1.254:53798
[2023/08/15 18:42:04.094886, 10, pid=4304, effective(0, 0), real(0, 0)] ../../source4/kdc/kdc-heimdal.c:81(kdc_process)
kdc_process: Received KDC packet of length 1949 from ipv4:10.32.1.254:53798
[2023/08/15 18:42:04.095384, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.095674, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.096019, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: TGS-REQ jhe@LMN.MEINE-SCHULE.DE from ipv4:10.32.1.254:53798 for HTTP/firewall@LMN.MEINE-SCHULE.DE [canonicalize, renewable]
[2023/08/15 18:42:04.098059, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.098928, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.099254, 6, pid=4304, effective(0, 0), real(0, 0)] ../../lib/util/util_ldb.c:58(gendb_search_v)
gendb_search_v: DC=lmn,DC=meine-schule,DC=de NULL -> 1
[2023/08/15 18:42:04.099418, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Server (HTTP/firewall@LMN.MEINE-SCHULE.DE) has no supported etypes
[2023/08/15 18:42:04.099459, 3, pid=4304, effective(0, 0), real(0, 0), class=kerberos] ../../source4/auth/kerberos/krb5_init_context.c:80(smb_krb5_debug_wrapper)
Kerberos: Failed building TGS-REP to ipv4:10.32.1.254:53798
[2023/08/15 18:42:04.099862, 3, pid=4304, effective(0, 0), real(0, 0)] ../../source4/samba/service_stream.c:67(stream_terminate_connection)
stream_terminate_connection: Terminating connection - 'kdc_tcp_call_loop: tstream_read_pdu_blob_recv() - NT_STATUS_CONNECTION_DISCONNECTED'
[2023/08/15 18:42:04.099917, 10, pid=4304, effective(0, 0), real(0, 0)] ../../lib/messaging/messages_dgm_ref.c:163(msg_dgm_ref_destructor)
msg_dgm_ref_destructor: refs=0x56087a21efc0
Darin lese ich als Fehlerursache v.a.
Kerberos: Client supported enctypes: aes256-cts-hmac-sha1-96, arcfour-hmac-md5, using aes256-cts-hmac-sha1-96/aes256-cts-hmac-sha1-96
Kerberos: ENC-TS Pre-authentication succeeded -- jhe@LMN.MEINE-SCHULE.DE using aes256-cts-hmac-sha1-96
Kerberos: Server (HTTP/firewall@LMN.MEINE-SCHULE.DE) has no supported etypes
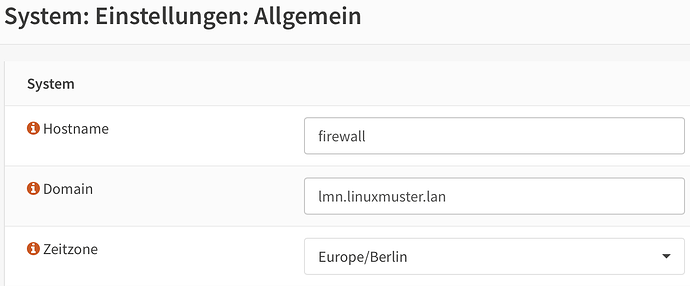
Die Opnsense-Seite passt zur dortigen /etc/krb5.conf:
[libdefaults]
default_realm = LMN.TGS-FREUDENSTADT.DE
dns_lookup_kdc = no
dns_lookup_realm = no
ticket_lifetime = 24h
default_keytab_name = /usr/local/etc/squid/squid.keytab
default_tgs_enctypes = aes256-cts-hmac-sha1-96 rc4-hmac des-cbc-crc des-cbc-md5
default_tkt_enctypes = aes256-cts-hmac-sha1-96 rc4-hmac des-cbc-crc des-cbc-md5
permitted_enctypes = aes256-cts-hmac-sha1-96 rc4-hmac des-cbc-crc des-cbc-md5
Nur auf der LMN7.2-Samba-Seite habe ich noch nicht gefunden, welche Encryptions dort verfügbar sind und wie und wo man die konfiguriert.
Kann es sein, dass sich OpnSense 23.7.1_3 und LMN 7.2 nicht mehr „verstehen“???
Schönen Abend!
Jens